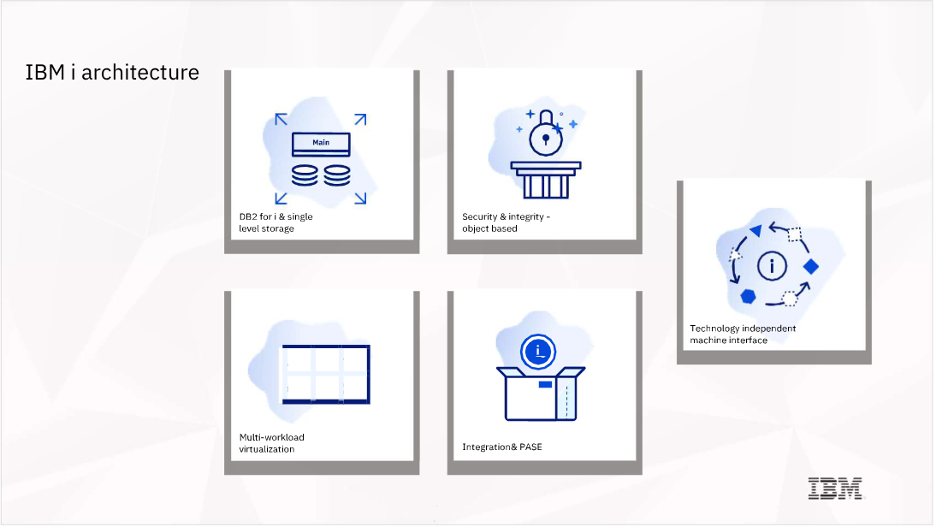
The adaptability of IBM i is guaranteed by an architecture that provides unique dependability, security, flexibility, and integration, all of which lead to a significant total cost of ownership advantage. There are five key pillars of this architecture that each provide clear differentiators from other operating systems. Together, they create the unique foundation for continuing innovation that exists today in IBM i 7.4:
1. Db2 for i and Single Level Storage
IBM i is unique among operating systems in how it treats data. Transactional workloads — the workloads that run the core business, such as financials, inventory control, and so on — are best served by relational databases. Most operating systems today deliver only a generic file system. Customers must then acquire, install, and manage a relational database. This is not the case with IBM i.
IBM i includes a fully relational, SQL-compliant database, Db2 for i, as an integrated piece of its architecture. In addition to being integrated, Db2 for i also automates many of the tasks typically performed by database administrators and storage administrators on other platforms. An example of this is rebalancing indexes over database tables. This is done in partnership with another unique part of IBM i, the single level storage architecture. The storage location for each piece of data is determined by the operating system, automating the analysis and placement of data to ensure high performance.

2. Security and Integrity
IBM i has several attributes that provide levels of integrity and data safety beyond other operating systems, but chief among them is the object-based architecture and hardware storage protection.
Object-based architecture means that every “thing” in IBM i comes with a predefined set of uses. For example, program objects have a predefined “use” that says programs may be executed, but files cannot. Security, built on top of the object-based architecture, guarantees that each “thing” in IBM i can only be used as its object type allows and nothing more. This key architectural design protects IBM i from “Trojan horse” attacks that plague other environments. A Trojan horse virus depends on a malicious piece of code masquerading as something else. For example, a program that deletes important information might appear to the user to be a photo or movie, but when that “file” is activated, the malicious program runs. This cannot happen with IBM i objects. A program cannot masquerade as something else.
Viruses, by contrast, often reach into existing programs and change the processor instructions. To accomplish this, the virus takes a pointer to some memory location and changes it to point somewhere else where it can insert unwanted instructions. IBM i, in conjunction with the POWER® processors, prevent this from happening. The unique single level storage architecture also allows enforcement of pointer manipulation so code from outside the operating system cannot change processor instructions.
These security and integrity features, along with many others, are not just added on to the operating system; they are built in by design.

3. Open Source Runtime and Integration of Technology
Over time, applications have required larger numbers of increasingly complex technologies to accomplish their tasks. IBM i integrates that technology — often described as middleware — into the operating system and its related integrated offerings, without requiring clients to purchase additional software.
Web servers, application servers, program integrity tools, digital certificate management, auditing capabilities, and directory and user identity services are all part of IBM i — built, tested, and delivered together. Additionally, as these technologies have evolved over time, IBM includes the latest and greatest into the IBM i portfolio.
An integral element of IBM i is the IBM Portable Application Solutions Environment for i (PASE). Technologically, PASE takes advantage of the capability of the POWER processors to run multiple flavors of operating systems at the same time, including IBM i and UNIX (AIX® and Linux). Using this POWER capability, IBM i has an AIX kernel embedded. It is the PASE environment that allows software, compiled for AIX, to be used directly by, and within, IBM i.
One of the most important uses of PASE within IBM i, however, is to bring open source components to the platform. Most open source development targets UNIX-flavoured operating environments, so finding or creating open source software that is ready to run in PASE requires very little work. This dramatically increases the number of solutions and software components available to IBM i
4. Multi-Workload Virtualization
Since the late 1990s, most businesses need their servers to do more than one thing. IBM i, from the very beginning, was designed to allow a client to run an Enterprise Resource Planning (ERP) solution on the same IBM i instance where payroll software, Customer Relationship Management (CRM) applications, and the web server are also running. The result was one server and one instance of the IBM i portfolio of products and multiple applications all running in one place.
However, IBM i is also designed to allow the running of the same software for multiple clients at the same time on the same machine. Using the built-in work management subsystem capabilities in conjunction with the inherent security capabilities of Db2 for i, IBM i can provide isolation of workloads. No client needs to ever interact with the data of the others. Using these built-in techniques long before “cloud” technology was widespread, ISVs that wrote solutions on IBM i were able to service multiple clients remotely, on one instance of IBM i.
This level of virtualization means fewer systems need to be purchased and fewer licenses and support contracts need to be bought, making IBM i a platform designed to give clients multi-workload management that drives a low total cost of ownership.
5. Investment Protection
Is it possible to imagine writing a business solution once and never again having to recompile it? IBM i clients don’t have to imagine it. This is what they’ve come to depend on through more than three decades. Application code that was written and compiled in the 1980s, which originally ran on a 48-bit, single-threaded processor, can run today, unchanged, on the latest POWER9™ multi-core, multi- threaded processors, and clients were not required to change the software or even need a recompile.
This unmatched forward compatibility is enabled through another unique architectural pillar of IBM i: the Technology Independent Machine Interface (TIMI). When a software program is compiled on IBM i, it is not compiled to specific processor instructions, as it would be on other operating systems. Instead, it is compiled to an intermediate set of instructions called MI instructions. This intermediate layer remains constant even when the layers of technology below them change. For example, as clients today move to POWER9 hardware, there is no need to recompile or retranslate application code. IBM i provides the translation of the existing MI instructions to the most current processor architecture.
An additional benefit to this unique technology is that IBM i can, and does, improve performance of user software over time, as the operating system engineers take advantage of the advancing capabilities of the Power Systems servers.
The architecture of IBM i has always been ahead of its time. In 1988, the architects put these key pillars in place with a vision of where computing might go in the future. As chip design, security, virtualization, mobile computing, and now AI have added sophistication to computing, the architecture of IBM i has allowed companies to grow and evolve knowing that IBM i has grown with them, providing the latest advancements while protecting critical business functions.
Subscribe to our newsletter to get notified about new blogs, product announcements, and security updates.